
Pebble Classic Battery Replacement
On Christmas day in 2013, I found a black Pebble smartwatch (now known as the Pebble Classic) under the Christmas tree. I was super excited about wearables such as Google Glass, and was thrilled to...

On Christmas day in 2013, I found a black Pebble smartwatch (now known as the Pebble Classic) under the Christmas tree. I was super excited about wearables such as Google Glass, and was thrilled to...

The radio spectrum is a complicated place, with many overlapping technologies and bands that vary depending on the regulatory domain. The radio spectrum is much too complicated to represent on a st...

In Hamina Network Planner, Attenuating Objects are used to represent solid objects such as warehouse shelves. They can be drawn either as rectangles or free-form shapes, and can have a custom lower...

If the Windows XP subreddit is a good indicator, it feels like Windows XP is entering a renaissance period. XP-era games are just old enough to be considered “vintage”, and there’s even new develop...

I have always loved small, portable devices. Over the years, I have owned and enjoyed many, always upgrading from device to device, carefully picking out each successor. For awhile now, I’ve wanted...

Ever since Atom was retired, I’ve been using Zed as my go-to simple text editor. While editing Markdown for this blog, I was annoyed that Zed didn’t seem to do word wrap, even though it understood ...

I originally wrote and posted this on Reddit, but have decided to duplicate all of my guides to my blog for centralization, and am taking the opportunity on 2026-03-22 to update it and fix broken l...

I originally wrote and posted this restoration log on TinkerDifferent, but have decided to duplicate all of my restoration logs to my blog for centralization. While I updated this post on 2025-07-0...
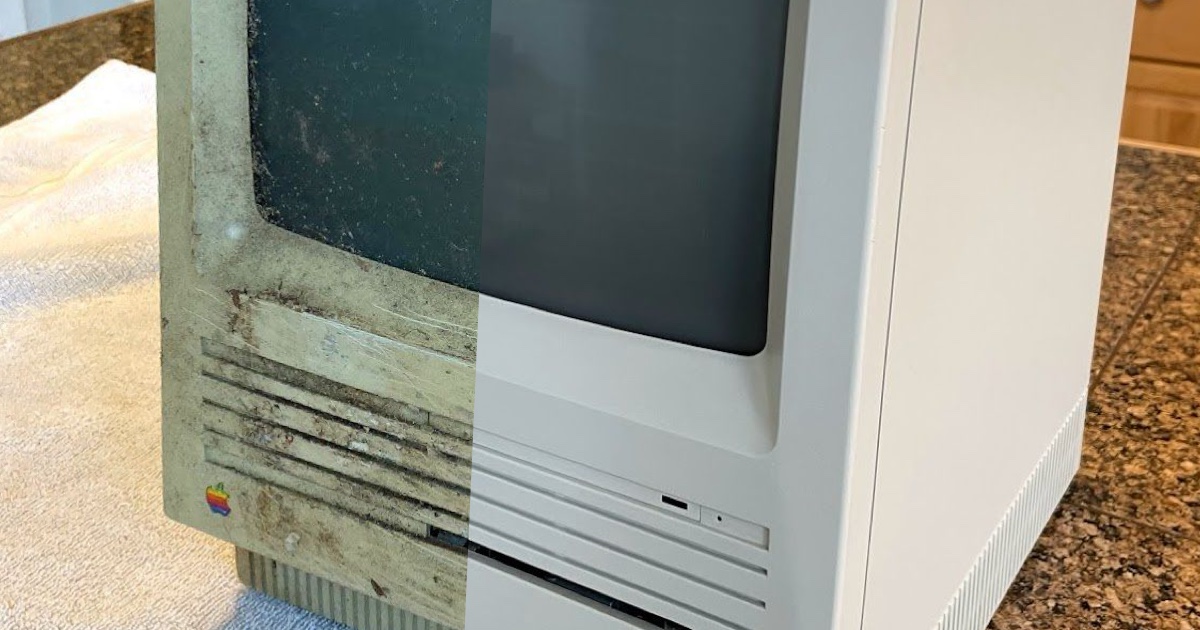
I originally wrote and posted this restoration log on TinkerDifferent, but have decided to duplicate all of my restoration logs to my blog for centralization. While I updated this post on 2025-07-0...

I originally wrote and posted this restoration log on 68kMLA, but have decided to duplicate all of my restoration logs to my blog for centralization. While I updated this post on 2026-03-22, the or...